There’s a quiet paradox at the heart of digital banking. The very features that make neobanks appealing—instant access, seamless onboarding, borderless transactions—also expand the attack surface. Every API call, every login attempt, every microsecond transaction introduces a potential vulnerability. Security, therefore, is not a layer added at the end. It is the foundation on which everything else rests.
For neobanks, security is not just about preventing breaches. It’s about preserving trust in an environment where customers never step into a physical branch. A single failure can ripple across user confidence, regulatory standing, and business continuity. That’s why the most successful neobanks don’t rely on one or two safeguards—they deploy a multi-layered security strategy that evolves continuously.
Below are nine proven strategies that form the backbone of secure neobank operations.
zero trust architecture as a default mindset
Traditional banking systems were built around the idea of a secure perimeter. Once inside, users and systems were largely trusted. That model no longer works in a distributed, cloud-native environment.
Zero Trust flips the model: nothing is trusted by default, whether inside or outside the network.
Core principles include:
- Verify every user and device continuously
- Enforce least-privilege access
- Segment systems to limit lateral movement
- Monitor all activity in real time
A simplified Zero Trust flow:
User Request → Identity Verification → Device Check → Access Decision → Continuous Monitoring
Here’s a comparison of traditional vs Zero Trust:
| Security Model | Trust Level | Risk Exposure | Adaptability |
|---|---|---|---|
| Perimeter-based | High (internal) | High | Low |
| Zero Trust | None (default) | Low | High |
For neobanks, Zero Trust is no longer optional—it is the baseline expectation.
strong authentication beyond passwords
Passwords alone are no longer sufficient. Neobanks must implement multi-factor authentication (MFA) and, increasingly, passwordless authentication methods.
Common authentication layers:
- One-time passwords (OTP)
- Biometric verification (fingerprint, face ID)
- Device-based authentication
- Behavioral biometrics
A layered authentication model:
| Layer Type | Example | Security Strength |
|---|---|---|
| Knowledge | Password/PIN | Low |
| Possession | Mobile device/OTP | Medium |
| Inherence | Biometrics | High |
Combining these layers significantly reduces unauthorized access.
end-to-end encryption and key management
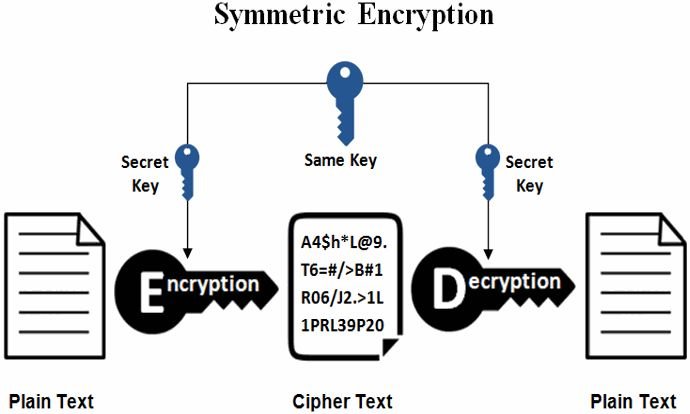
Encryption is the backbone of data security. But simply encrypting data is not enough—key management is equally critical.
Neobanks must ensure:
- Data encryption in transit (TLS)
- Data encryption at rest
- Secure key storage (HSMs or vaults)
- Regular key rotation
A basic encryption lifecycle:
Data → Encryption → Storage → Access via Key → Decryption
Encryption effectiveness depends on how well keys are protected. Weak key management can render strong encryption useless.
real-time fraud detection and behavioral analytics
Fraud detection has evolved from rule-based systems to intelligent, adaptive models. Modern neobanks analyze user behavior continuously to detect anomalies.
Key indicators include:
- Unusual transaction patterns
- Sudden location changes
- Device switching
- Transaction velocity spikes
Example behavioral risk table:
| Behavior Pattern | Risk Level | Action Taken |
|---|---|---|
| Login from new country | High | Trigger MFA |
| Rapid transfers | High | Temporary account freeze |
| Normal usage | Low | Allow transaction |
Real-time detection allows neobanks to act before damage occurs, rather than after.
secure API architecture and monitoring

APIs are the backbone of neobank infrastructure, connecting apps, partners, and services. However, they are also prime targets for attackers.
API security strategies include:
- Authentication (OAuth 2.0, API keys)
- Rate limiting
- Input validation
- Continuous monitoring
A simplified API security flow:
Client → API Gateway → Authentication → Validation → Service
API vulnerabilities can expose entire systems, making this area a top priority.
data minimization and privacy-first design
One of the most effective security strategies is simple: collect less data. The less sensitive data a system stores, the lower the risk.
Principles of data minimization:
- Collect only necessary information
- Limit data retention periods
- Anonymize or tokenize sensitive data
- Restrict internal access
Data lifecycle model:
Collection → Usage → Storage → Deletion
Reducing data exposure not only enhances security but also simplifies compliance with privacy regulations.
incident response and recovery planning
No system is immune to breaches. What matters is how quickly and effectively a neobank responds.
A strong incident response plan includes:
- Detection and alert systems
- Defined response teams
- Communication protocols
- Recovery and remediation steps
Incident response timeline:
| Timeframe | Action |
|---|---|
| 0–1 hour | Detect and isolate issue |
| 1–24 hours | Investigate and contain |
| 24–72 hours | Notify stakeholders |
| 72+ hours | Recover and strengthen systems |
Preparedness can significantly reduce the impact of security incidents.
employee access control and insider threat management
Not all threats come from outside. Insider risks—whether malicious or accidental—are a significant concern.
Key controls include:
- Role-based access control (RBAC)
- Activity monitoring
- Access audits
- Separation of duties
Access control matrix example:
| Role | Access Level | Restrictions |
|---|---|---|
| Developer | System-level | No access to customer data |
| Support agent | Limited data view | No transaction authority |
| Admin | Full access | Logged and monitored |
Limiting access reduces the potential damage from insider threats.
continuous security testing and penetration audits
Security is not static. Systems must be tested continuously to identify vulnerabilities.
Testing methods include:
- Penetration testing
- Vulnerability scanning
- Bug bounty programs
- Red team exercises
Testing frequency table:
| Test Type | Frequency |
|---|---|
| Vulnerability scan | Weekly |
| Penetration test | Quarterly |
| Full security audit | Annually |
Regular testing ensures that defenses evolve alongside threats.
security awareness and customer education
Even the most secure systems can be compromised by human error. Educating users and employees is a critical layer of defense.
Key initiatives:
- Phishing awareness campaigns
- Secure password practices
- App security guidelines
- Real-time alerts for suspicious activity
Customer awareness example:
| Scenario | Recommended Action |
|---|---|
| Suspicious email | Do not click links |
| Unknown login alert | Change password immediately |
| OTP request | Never share with anyone |
Security is a shared responsibility between the institution and its users.
integrated security architecture overview
Below is a simplified view of how these strategies work together:
User → Authentication → API Layer → Transaction Processing → Fraud Detection → Logging → Monitoring → Incident Response
Each layer reinforces the others, creating a defense-in-depth model.
security maturity model for neobanks
| Stage | Characteristics | Security Level |
|---|---|---|
| Early | Basic controls, manual processes | Low |
| Growth | Automated tools, partial integration | Medium |
| Advanced | Fully integrated, real-time systems | High |
Neobanks must aim to move quickly toward advanced maturity.
common security gaps to avoid
Despite best intentions, many startups fall into predictable traps:
- Over-reliance on passwords
- Ignoring API vulnerabilities
- Lack of incident response planning
- Weak access controls
- Infrequent security testing
Addressing these gaps early can prevent major issues later.
final perspective
Security in neobanking is not a destination—it is a continuous process. Threats evolve, technologies change, and user behaviors shift. The most resilient neobanks are those that treat security as a living system, constantly adapting and improving.
By implementing these nine strategies, startups can build a strong foundation that not only protects assets but also earns customer trust. In a world where digital trust is fragile, security becomes the ultimate differentiator.
frequently asked questions
- what is the most important security strategy for neobanks
Zero Trust architecture is often considered the most critical because it enforces strict verification across all systems and users. - how do neobanks detect fraud in real time
They use behavioral analytics and machine learning models to monitor transactions and identify anomalies instantly. - are biometrics safe for authentication
Yes, when implemented correctly, biometrics provide a high level of security, especially when combined with other authentication factors. - how often should security testing be conducted
Vulnerability scans should be frequent (weekly), while penetration tests are typically conducted quarterly. - can small neobanks afford advanced security systems
Many modern security tools are scalable and cloud-based, making them accessible even for startups. - what role do customers play in security
Customers play a crucial role by following best practices, such as not sharing OTPs and recognizing phishing attempts.
