Security in a neobank doesn’t usually fail in dramatic, cinematic ways. It fails quietly—through small gaps, overlooked assumptions, and systems that worked fine yesterday but aren’t built for today’s scale.
What makes this tricky is speed. Most teams don’t have the luxury of long, complex security overhauls. They need fixes that are fast, practical, and immediately reduce risk without breaking the product.
This article walks through six security fixes that do exactly that. These are not theoretical frameworks or enterprise-only strategies. They are grounded, field-tested improvements that can be implemented quickly and start delivering results almost immediately.
fix 1: enforce adaptive multi-factor authentication (mfa)
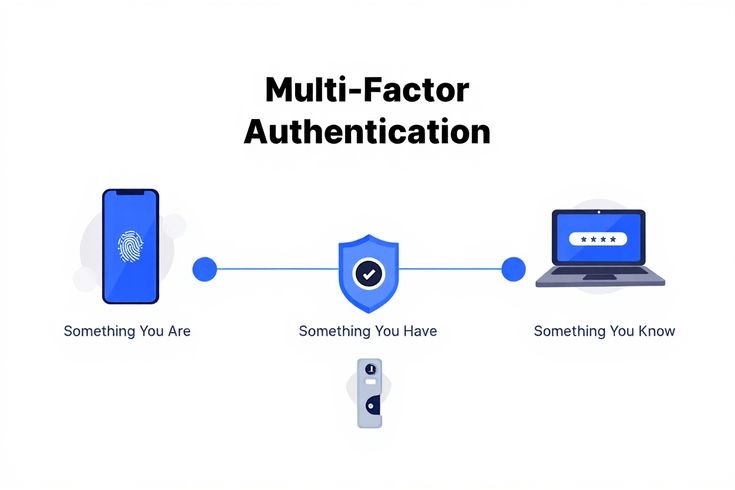
If there’s one fix that consistently delivers immediate security gains, it’s strengthening authentication.
But not just basic MFA—adaptive MFA.
Instead of forcing every user through the same authentication flow, adaptive MFA adjusts based on risk signals like:
- New device login
- Unusual location
- High-value transaction
- Behavioral anomalies
table: static vs adaptive mfa
| Feature | Static MFA | Adaptive MFA |
|---|---|---|
| User experience | Same for all users | Risk-based prompts |
| Security level | Moderate | High |
| Fraud prevention | Limited | Strong |
| Friction | High | Optimized |
simple risk flow chart:
Login Attempt → Risk Evaluation →
Low Risk → Password Only
Medium Risk → OTP Required
High Risk → OTP + Device Verification
quick implementation steps:
- Integrate device fingerprinting
- Add IP/geolocation checks
- Trigger MFA only when risk thresholds are exceeded
impact:
Teams often see immediate drops in account takeover attempts—sometimes by over 50%.
fix 2: lock down api access with strict controls
APIs are the backbone of neobanks. They are also one of the most common attack surfaces.
The issue is rarely that APIs exist—it’s that they are too permissive.
table: common api vulnerabilities
| Vulnerability | Description |
|---|---|
| Weak authentication | Missing or insecure tokens |
| Excessive permissions | Users access more than needed |
| Rate limit absence | No control over request volume |
| Poor logging | No visibility into abuse |
quick security checklist:
| Control | Status (Yes/No) |
|---|---|
| OAuth2 implemented | |
| Rate limiting active | |
| API gateway in place | |
| Access logs stored |
chart: api risk reduction
No Controls → High Risk
Basic Controls → Medium Risk
Strict Controls → Low Risk
fast fixes:
- Implement rate limiting immediately
- Restrict endpoints by role
- Use short-lived access tokens
result:
You reduce both automated attacks and accidental misuse in a matter of days.
fix 3: monitor transactions in real time, not after the fact

Many systems still rely on post-transaction analysis. By the time fraud is detected, the money is already gone.
Real-time monitoring changes that dynamic.
table: monitoring approaches
| Approach | Detection Timing | Risk Level |
|---|---|---|
| Batch processing | After transaction | High |
| Near real-time | Minutes later | Medium |
| Real-time | Before completion | Low |
simple monitoring flow:
Transaction Initiated → Risk Score Calculated →
Low Risk → Approve
High Risk → Block or Review
fast deployment ideas:
- Add rule-based triggers (e.g., unusual amount, velocity spikes)
- Use pre-built fraud detection tools
- Start with high-risk transaction categories
impact chart:
Before:
Fraud Detection Lag → High Losses
After:
Instant Detection → Reduced Losses
fix 4: secure sensitive data with practical encryption upgrades
Encryption often exists—but not always where it matters most.
Common gaps:
- Data encrypted at rest but not in transit
- Weak key management
- Hardcoded credentials
table: encryption gaps
| Area | Common Issue | Fix |
|---|---|---|
| Data in transit | No TLS enforcement | Enforce HTTPS everywhere |
| Data at rest | Partial encryption | Full database encryption |
| Key management | Static keys | Rotate keys regularly |
| Credentials | Stored in code | Use secure vaults |
quick wins:
- Enforce TLS 1.2+ across all endpoints
- Move secrets to a secure vault
- Enable automatic key rotation
chart: data exposure risk
No Encryption → Critical Risk
Partial Encryption → Moderate Risk
Full Encryption → Low Risk
result:
Even if a breach occurs, the data becomes significantly harder to exploit.
fix 5: implement strict access control for internal systems
One of the most underestimated risks comes from inside—misconfigured access controls.
Employees, contractors, and systems often have more access than necessary.
table: access control issues
| Issue | Risk Level | Example |
|---|---|---|
| Over-permission | High | Developer accessing user data |
| Shared accounts | High | No accountability |
| No role separation | Medium | Same user approves and executes |
| Inactive accounts | High | Former employee access |
access control model:
User → Role Assignment → Permission Scope → Activity Logging
fast fixes:
- Implement role-based access control (RBAC)
- Remove unused accounts
- Enforce least privilege principle
chart: insider risk reduction
No Control → High Risk
Basic RBAC → Medium Risk
Strict RBAC + Logging → Low Risk
impact:
This reduces both accidental misuse and intentional abuse almost immediately.
fix 6: enable continuous security logging and alerting
You can’t fix what you can’t see.
Many neobanks log events—but don’t actively monitor them.
table: logging maturity levels
| Level | Description |
|---|---|
| Level 1 | Logs stored, not reviewed |
| Level 2 | Periodic manual review |
| Level 3 | Automated alerts |
| Level 4 | Real-time monitoring + response |
quick logging checklist:
| Event Type | Logged (Yes/No) |
|---|---|
| Login attempts | |
| Failed transactions | |
| API access | |
| Permission changes |
simple alert flow:
Event Triggered → Log Captured → Alert Generated → Action Taken
fast improvements:
- Set up alerts for unusual activity
- Use centralized logging systems
- Define response playbooks
result:
Incidents are detected faster, often before they escalate.
putting it all together
These six fixes are powerful individually—but their real strength comes from working together.
summary table
| Fix # | Focus Area | Speed of Implementation | Impact Level |
|---|---|---|---|
| 1 | Adaptive MFA | Fast | Very High |
| 2 | API security | Fast | High |
| 3 | Real-time monitoring | Medium | Very High |
| 4 | Encryption upgrades | Fast | High |
| 5 | Access control | Fast | High |
| 6 | Logging & alerting | Fast | Very High |
combined effect chart:
Single Fix → Moderate Improvement
Multiple Fixes → Strong Protection
All Six → Layered Security
The key idea here is layering. No single fix makes you secure—but together, they dramatically reduce risk.
practical implementation roadmap
If you’re short on time and resources, here’s a simple rollout plan:
week 1:
- Enforce MFA
- Enable basic logging
week 2:
- Add API rate limiting
- Clean up access controls
week 3:
- Implement real-time monitoring rules
- Upgrade encryption practices
table: rollout plan
| Week | Priority Actions |
|---|---|
| Week 1 | MFA + Logging |
| Week 2 | API + Access Control |
| Week 3 | Monitoring + Encryption |
This staged approach allows quick wins while building toward a stronger security posture.
faqs
- what is the fastest security improvement a neobank can implement?
Adaptive MFA is usually the fastest and most impactful fix. It can be deployed quickly and significantly reduces account takeover risks.
- do small neobanks really need advanced security systems?
Yes, but they don’t need to build everything from scratch. Many third-party tools provide scalable security solutions that can be implemented بسرعة.
- how important is real-time monitoring compared to batch processing?
Real-time monitoring is critical for preventing fraud before it happens, while batch processing only helps detect it after the damage is done.
- can security fixes affect user experience?
They can, but adaptive approaches (like risk-based MFA) minimize friction while maintaining strong protection.
- how often should security systems be reviewed?
Ideally, continuously. At minimum, perform monthly reviews and immediate checks after any major system changes.
- what is the biggest security mistake neobanks make?
Relying on a single layer of defense. Strong security comes from combining multiple controls—authentication, monitoring, encryption, and access management.
In the end, security isn’t about building the perfect system. It’s about reducing risk quickly, consistently, and intelligently.
These six fixes won’t make your neobank invulnerable—but they will make it significantly harder to break. And in today’s environment, that difference matters more than ever.

