Speed has become a defining factor in modern security practices. Organizations no longer have the luxury of waiting weeks for audit results while threats evolve in real time. Whether it’s a fintech startup, a SaaS platform, or an enterprise infrastructure, the ability to run fast, reliable security audits can mean the difference between early detection and costly breaches.
Fast security audit tools are designed to deliver immediate insights without sacrificing depth. They automate repetitive checks, surface vulnerabilities quickly, and allow teams to act before issues escalate. But speed alone is not enough—the real value lies in accuracy, integration, and usability.
This article explores twelve fast security audit tools that deliver instant results, along with practical insights, comparison tables, and implementation strategies.
understanding the need for fast security audits
Security audits were traditionally periodic exercises. Today, they are continuous processes embedded into daily operations. This shift is driven by:
- Increasing cyber threats
- Complex cloud environments
- Continuous deployment pipelines
- Regulatory pressure
A fast audit tool must meet three criteria:
| Criteria | Description |
|---|---|
| Speed | Produces results in minutes or hours |
| Accuracy | Minimizes false positives |
| Integration | Works with existing systems |
Organizations that adopt fast audit tools gain visibility, reduce risk, and improve response times.
tool 1: automated vulnerability scanners
Automated vulnerability scanners are often the first line of defense. They scan systems, applications, and networks to identify known vulnerabilities.
Key features include:
- Rapid scanning of large environments
- Database of known vulnerabilities (CVEs)
- Prioritized risk reporting
Example output structure:
| Vulnerability | Severity | Suggested Fix |
|---|---|---|
| Outdated library | High | Update version |
| Open port | Medium | Restrict access |
| Weak cipher | Low | Upgrade protocol |
These tools provide immediate insights, making them essential for quick audits.
tool 2: configuration auditing tools
Misconfigurations are one of the leading causes of security incidents. Configuration audit tools check systems against best practices and compliance benchmarks.
Common checks:
- Firewall settings
- Access permissions
- System hardening standards
Configuration risk levels:
| Configuration State | Risk |
|---|---|
| Misconfigured | High |
| Partially compliant | Medium |
| Fully compliant | Low |
These tools are especially useful in cloud environments where configurations change frequently.
tool 3: web application scanners
Web applications are frequent targets for attackers. Web scanners identify vulnerabilities such as SQL injection, cross-site scripting (XSS), and insecure headers.
Scanning capabilities:
- URL crawling
- Input testing
- Response analysis
Sample findings:
| Issue | Impact |
|---|---|
| SQL injection | Data breach |
| XSS | Session hijacking |
| Missing headers | Security gaps |
Fast web scanners allow developers to fix issues before deployment.
tool 4: dependency and code analysis tools
Modern applications rely heavily on third-party libraries. Dependency analysis tools scan codebases to identify vulnerable components.
Capabilities:
- Open-source vulnerability detection
- License compliance checks
- Version tracking
Dependency risk chart:
| Dependency Status | Risk |
|---|---|
| Up-to-date | Low |
| Slightly outdated | Medium |
| Deprecated | High |
These tools integrate seamlessly into development pipelines for continuous auditing.
tool 5: identity and access audit tools
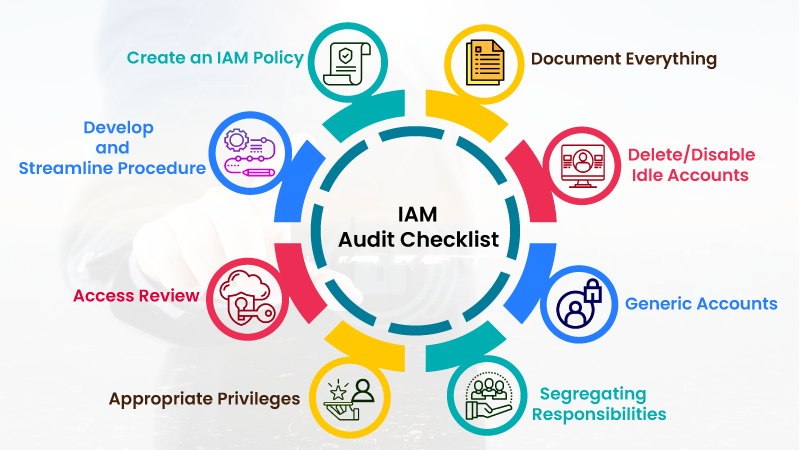
Access control is a critical security layer. Identity audit tools analyze who has access to what—and whether it is justified.
Audit focus areas:
- Privileged accounts
- Role assignments
- Access anomalies
Access risk matrix:
| Access Type | Risk |
|---|---|
| Least privilege | Low |
| Excessive access | High |
| Orphan accounts | Critical |
Quick audits in this area can prevent insider threats and unauthorized access.
tool 6: network security scanners
Network scanners map and analyze network structures to identify vulnerabilities.
Functions include:
- Port scanning
- Service detection
- Network mapping
Network exposure levels:
| Exposure | Risk |
|---|---|
| Minimal | Low |
| Moderate | Medium |
| Extensive | High |
Fast scanning helps teams understand their attack surface instantly.
tool 7: endpoint security audit tools
Endpoints such as laptops, mobile devices, and servers are common entry points for attackers.
Endpoint audit tools check:
- Antivirus status
- Patch levels
- Device compliance
Endpoint health overview:
| Status | Risk |
|---|---|
| Fully updated | Low |
| Partially patched | Medium |
| Unpatched | High |
These tools are critical in remote and hybrid work environments.
tool 8: cloud security posture management tools
Cloud environments require specialized auditing tools. Cloud security posture management (CSPM) tools provide real-time visibility into cloud configurations.
Core features:
- Continuous monitoring
- Compliance checks
- Risk prioritization
Cloud risk comparison:
| Posture | Risk |
|---|---|
| Secure | Low |
| Misconfigured | High |
CSPM tools are essential for maintaining secure cloud operations.
tool 9: log analysis and monitoring tools
Logs provide valuable insights into system activity. Log analysis tools process large volumes of data to detect anomalies.
Capabilities:
- Real-time monitoring
- Pattern detection
- Alert generation
Log analysis workflow:
| Step | Function |
|---|---|
| Collection | Gather logs |
| Processing | Analyze data |
| Alerting | Flag issues |
Fast log analysis enables immediate threat detection.
tool 10: penetration testing automation tools
Penetration testing tools simulate attacks to identify vulnerabilities.
Automation features:
- Predefined attack scenarios
- Rapid execution
- Detailed reporting
Pen test results:
| Finding | Severity |
|---|---|
| Exploitable vulnerability | High |
| Weak configuration | Medium |
These tools provide quick insights into real-world attack scenarios.
tool 11: compliance auditing tools
Compliance tools ensure adherence to standards such as ISO, PCI-DSS, and GDPR.
Audit coverage:
- Policy checks
- Documentation review
- Control validation
Compliance status:
| Status | Meaning |
|---|---|
| Compliant | Meets standards |
| Partial | Needs improvement |
| Non-compliant | High risk |
Fast compliance audits reduce regulatory risks.
tool 12: security information and event management systems
SIEM systems aggregate data from multiple sources to provide a centralized view of security events.
Core functions:
- Data correlation
- Threat detection
- Incident response
SIEM effectiveness:
| Capability | Benefit |
|---|---|
| Real-time alerts | Immediate response |
| Data aggregation | Better visibility |
SIEM tools tie together insights from all other audit tools.
integrated security audit framework
To achieve instant results, organizations must integrate these tools into a unified framework.
| Layer | Tool Type | Purpose |
|---|---|---|
| Infrastructure | Network scanners | Identify exposure |
| Application | Web scanners | Detect vulnerabilities |
| Code | Dependency tools | Secure software |
| Access | Identity audits | Control permissions |
| Monitoring | SIEM | Central oversight |
Integration ensures that insights from one tool enhance others.
comparison chart: speed vs depth of audit tools
| Tool Type | Speed | Depth |
|---|---|---|
| Vulnerability scanners | High | Medium |
| Web scanners | High | High |
| Code analysis | Medium | High |
| SIEM | Medium | Very high |
This chart highlights the trade-off between speed and depth.
implementation strategy for instant results
Organizations should adopt a phased approach:
| Phase | Focus |
|---|---|
| Phase 1 | Quick wins (scanners, config tools) |
| Phase 2 | Integration (SIEM, logging) |
| Phase 3 | Advanced tools (AI, automation) |
Automation is key to achieving instant results.
common challenges and solutions
| Challenge | Solution |
|---|---|
| Too many alerts | Prioritize risks |
| Tool overlap | Consolidate platforms |
| Integration issues | Use APIs |
Addressing these challenges ensures effective use of tools.
conclusion
Fast security audit tools have redefined how organizations approach risk management. Instead of periodic reviews, businesses can now achieve continuous visibility and instant insights.
The twelve tools discussed here form a comprehensive toolkit for identifying vulnerabilities, ensuring compliance, and strengthening defenses. When integrated effectively, they create a powerful security ecosystem capable of adapting to modern threats.
Speed, however, must be balanced with accuracy and strategy. The goal is not just to detect issues quickly, but to resolve them efficiently and prevent recurrence.
frequently asked questions
- what are fast security audit tools
They are tools designed to quickly identify vulnerabilities and security issues, often delivering results in real time or within minutes. - can small businesses use these tools effectively
Yes, many tools are scalable and suitable for organizations of all sizes. - how often should security audits be performed
Ideally, audits should be continuous, supported by automated tools. - do fast tools compromise accuracy
Not necessarily, but proper configuration and tuning are essential to maintain accuracy. - what is the role of automation in security audits
Automation speeds up processes, reduces human error, and enables continuous monitoring. - how do these tools work together
They integrate into a layered security framework, where each tool addresses a specific aspect of security.
By adopting these tools and strategies, organizations can move from reactive security practices to proactive, real-time defense systems.
