Every 39 seconds, there is a hacker attack somewhere in the world.
For neobanks and digital wallets, that’s more than a scary statistic. It’s a daily reality. These days, millions of people use apps to store, send and spend money. And where the money goes, fraud will follow.
The challenge is: how do we stop fraudsters before they inflict maximum damage?
The solution is fraud detection — a collection of smart, technology-enabled techniques that are woven into the security audit process. These methods don’t just respond to fraud. They predict it. They prevent it. And they shield the people who invest their hard-earned money using these platforms.
In this article, you will learn 11 actionable fraud detection methods that are being applied to neobank and digital wallet security audits right now. No fluff. No jargon. Just simple, useful information that helps you understand how the system works — and whether your money is actually safe.
Why Fraud Detection Is the Pulse of Every Security Audit
Security audits are not checkbox exercises. They are intense, systematic inquiries into how effectively a platform can detect and block fraud.
For neobanks in particular, fraud detection is especially important. Neobanks do not have in-person verification like traditional banks. Everything happens online. That opens the door for more fraudsters to get through.
It is estimated that by 2027, digital payment fraud losses will surpass $40 billion worldwide. That figure really should make everyone sit up straight.
Security audits consider whether a neobank’s fraud prevention systems are robust enough to protect against real-life threats. They test, probe and stress-test all levels of security.
Now let’s delve into what those layers actually are.
1. Machine Learning Models — Training Computers to Identify the Bad Guys
Most contemporary fraud detection systems are fueled by machine learning.
Here’s the simple version of how it works. The system learns the contours of what “normal” looks like for each user. It analyzes thousands of data points — the size of your typical transaction, your average login time, the device from which you always connect.
Then, when something deviates from that pattern, the system flags it.
What Makes ML So Effective
Rule-based legacy systems say things like “flag any transaction greater than $10,000.” Machine learning goes much deeper. It can pick up on a $200 transaction that seems perfectly normal on paper but takes place at 4 AM from a new device in another country.
In a security audit, testers check for:
- How well the ML model is able to identify fraud with few false positives
- Speed of model adaptation to new fraud patterns
- Whether the model has been trained on real-world, diverse data sources
- How the system handles edge cases and unusual but legitimate transactions
Platforms like Stripe Radar, Feedzai and DataVisor utilize sophisticated ML models designed specifically for financial fraud detection.
2. Velocity Checks — Catching Fraudsters Who Move Too Fast

Speed kills — and in the realm of fraud, it tends to be a dead giveaway.
Velocity checks track how fast a user is performing actions. If somebody makes 50 transactions in a five-minute period, or tries 30 different card numbers in sequence — something is going very wrong.
How Velocity Checks Work
The system tallies actions over short time windows — seconds, minutes, hours. It measures:
- Number of transactions per minute
- Login attempts per hour
- Number of payees added in a single session
- Number of password reset requests per day
When any of these reach a suspicious threshold, the system will block, throttle or flag the activity.
What Auditors Look For
Testers perform simulated velocity attacks during fraud detection audits. They check whether the platform catches fast-paced activity and whether thresholds are calibrated at just the right sensitivity — not too tight (which turns off legitimate users) and not too loose (which lets fraudsters through).
3. Device Fingerprinting — Knowing Your Device Better Than You Do
Each device that connects to a neobank is given an individual identity. Device fingerprinting picks that identity up silently in the background.
It collects data points like:
- Device type and model
- Operating system version
- Browser or app version
- Screen resolution
- IP address and geolocation
- Installed fonts and plugins
Why It Matters for Fraud Detection
When someone is committing fraud via a stolen login, they are almost certainly using a different device. Device fingerprinting immediately captures that mismatch.
If your account has only ever been accessed from an iPhone 14 in Karachi, and suddenly somebody logs in on an old Android tablet somewhere in Eastern Europe — that’s a warning signal. The system triggers a further layer of validation before allowing that session to proceed.
Security audits verify that fingerprinting is implemented correctly and whether it can be bypassed by advanced attackers using virtual machines or emulators.
4. Geolocation Analysis — Tracking the Money Across the Map
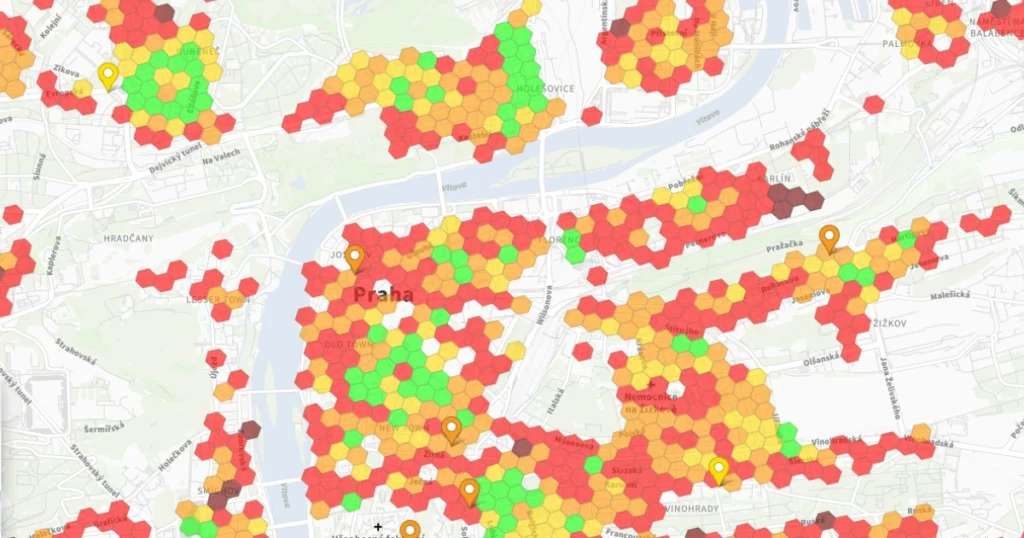
Where you are matters as much as what you are doing.
Geolocation analysis follows the geographic location of logins and transactions. When the location doesn’t fit expected patterns, the fraud detection system kicks in.
The Impossible Travel Scenario
One of the oldest fraud signals is what analysts call “impossible travel.” This is when a person seemingly signs in from New York at 9 AM and then from Tokyo at 9:15 AM.
That’s physically impossible. It means one of those logins was not really the account owner.
What Gets Tested in Audits
Auditors mimic impossible travel and location-spoofing attempts using VPNs and proxy servers. They check whether the system:
- Correctly identifies suspicious location jumps
- Handles VPN usage while still allowing legitimate users who use VPNs for privacy
- Responds with step-up authentication rather than just a hard block
| Geolocation Signal | Fraud Risk Level |
|---|---|
| New country login | High |
| Impossible travel | Critical |
| VPN or proxy use | Medium |
| Consistent home location | Low |
| Sudden city change | Medium-High |
5. Behavioral Biometrics — The Way You Touch Your Screen Tells a Story
This is one of the most fascinating fraud detection methods in present-day security audits.
Behavioral biometrics do more than just confirm who you are. They verify how you act.
The system detects even the tiniest details:
- The pace and rhythm of your typing
- How firmly you press down on the screen
- The angle at which you hold your phone
- What scrolling through the app looks like
- How you navigate between screens
Why a Fraudster Can’t Pull This Off
Even if somebody steals your password, your PIN and your phone, they still don’t move exactly as you do. Their muscle memory is different. Their typing patterns are different.
Behavioral biometrics builds a unique “behavioral fingerprint” for each user. Any discrepancy from that fingerprint, even a minor one, sets off an alert.
According to BioCatch, a global leader in this technology, behavioral biometrics can identify account takeover fraud with more than 90% accuracy.
During a security audit, testers check how the system responds when an attacker tries to copy how real users behave — a technique known as behavioral replay attacks.
6. Transaction Pattern Analysis — Reading the Financial Story
Everyone has a money story. And that story has patterns.
You likely buy groceries every week. You pay rent once a month. You get coffee from the same place every morning. These habits create a financial fingerprint.
Transaction pattern analysis is the art of studying those habits and flagging anything that strays from them.
What Looks Suspicious
- A sudden large transfer to an unfamiliar account
- Numerous small transactions just shy of the reporting threshold (a process known as structuring)
- Purchases from merchants in categories you’ve never used before
- Fast movement of funds in and out of the account
How Auditors Put This System Through Its Paces
Security auditors stress-test transaction pattern systems using real-world fraud scenarios. They verify that the system is detecting structuring attempts, money mule patterns and account takeover spending sprees.
The idea is to see how well the system can catch a fraudster attempting to blend in slowly, rather than hitting hard and fast.
7. Identity Verification Checks — Making Sure You Are Really You
Fraud often starts right at the beginning — when someone opens an account with stolen or fabricated identity documents.
Identity verification (IDV) checks are a fundamental fraud detection method, and security audits spend serious time assessing how strong they are.
Layers of Identity Verification
Document verification — The system scans government-issued IDs and checks for authenticity. It looks at security features, fonts, holograms and formatting compared to known templates.
Facial recognition — The user snaps a selfie, and the system matches it against the photo on their identity document. Liveness detection verifies the user is a real, live person — not a printed photo or video replay.
Database screening — The platform checks the user’s credentials against fraud databases, sanctions lists and politically exposed persons (PEP) lists.
What Auditors Test
Fraud detection audits crawl over each part of the IDV process. Testers try to use:
- Doctored ID documents
- Deep-fake selfie videos
- Synthetic identities constructed from real-but-stolen data points
If the system successfully detects these attacks, it passes. If it doesn’t, the neobank has a serious problem.
8. AML Screening and Monitoring — Stopping Dirty Money at the Door
AML screening is both a legal requirement and a very effective method of detecting fraud.
Money laundering is the process of making illegally obtained money look legitimate. Neobanks and digital wallets are particularly appealing targets for launderers — they’re fast, purely digital and sometimes only lightly regulated.
How AML Screening Works
Customer screening — Every new customer is vetted against global watchlists, sanctions lists and adverse media databases before being allowed to open an account.
Transaction monitoring — Continuous examination looks for classic money laundering patterns like placement (pouring cash into the banking system), layering (moving money through various accounts to conceal its origin) and integration (using the cleaned cash in legitimate transactions).
Suspicious Activity Reports (SARs) — When the system raises a red flag, it generates a SAR that is reviewed by a compliance officer and may be reported to regulators.
What Security Auditors Examine
| AML Check | What It Covers |
|---|---|
| Sanctions screening | OFAC, UN, EU blacklists |
| PEP screening | Politically exposed persons |
| Adverse media | Negative news coverage |
| Transaction monitoring | Layering and structuring patterns |
| SAR generation | Accuracy and timeliness of reports |
Auditors test whether AML systems can catch subtle laundering schemes — not just obvious ones. They also check whether the system generates too many false positives, which can burden compliance teams and create friction in operations.
9. Social Engineering Detection — Spotting the Human Hack
Not all fraud involves code. Some of the most effective attacks target people directly.
Social engineering is when a fraudster manipulates a real user into handing over money or account access. Think fabricated customer support calls, phishing emails or WhatsApp scams that purport to come from the bank.
How Neobanks Identify Social Engineering Fraud
Social engineering is more difficult to detect than technical attacks. The user is making voluntary movements. But there are signals.
- Unusual transactions immediately after a phone call
- Large transfers to new payees with whom the customer has no previous relationship
- The user accessing the app from a location inconsistent with their normal behavior
- Actions happening at an abnormal pace, as if someone on the other end of a phone was directing them
What Auditors Look For
Security audits test whether the platform has:
- Warm transfer alerts before large transfers to new payees
- Delay periods on first-time large transactions
- In-app alerts when users are about to send money to a new account
- Outbound call verification systems to confirm questionable activity
The UK’s APP (Authorized Push Payment) fraud problem has pushed regulators to demand these controls across all digital payment platforms.
10. Network Analysis and Link Detection — Unraveling the Web of Fraud
Individual transactions can look innocent. But zoom out and look at a network of accounts, and an entirely different picture can appear.
Network analysis charts how accounts, devices, phone numbers and IP addresses relate to each other. It seeks clusters of linked entities that might reflect organized fraud rings.
Real-World Example
Imagine 50 accounts that all originated from the same IP address, all used the same mobile device model and all received small deposits before transferring money to one external account. Each individual account may seem fine. But the network pattern tells a very different story — it screams fraud ring.
Tools Used in Network Analysis
Graph-based analytics platforms like Neo4j, Quantexa and SAS Fraud Management are purpose-built for this type of link analysis.
During security audits, testers evaluate whether the neobank’s network analysis system can:
- Connect accounts across multiple data points (not just the obvious ones)
- Detect mule account networks
- Spot synthetic identity clusters
- Generate alerts when suspicious networks grow beyond a certain size
For a broader look at how leading neobanks and digital finance platforms compare on security features, BankProfi is a trusted resource for researching and evaluating your options.
11. Real-Time Decisioning Engines — Making Fraud Calls in Milliseconds
All the fraud detection techniques above generate signals. But something needs to act on those signals instantly.
That’s the job of the real-time decisioning engine.
How It Works
A decisioning engine sits at the center of the fraud detection stack. It receives inputs from every other system — ML models, velocity checks, behavioral biometrics, geolocation — and makes a decision in real time.
That decision might be:
- Allow the transaction
- Block the transaction
- Request step-up authentication (like a fingerprint scan or OTP)
- Flag for human review
All of this happens in under 200 milliseconds. Faster than a blink.
What Auditors Stress-Test
Security auditors run high-volume load tests to make sure the decisioning engine performs under pressure. They check:
- How the system behaves during peak transaction periods
- Whether latency increases during high load
- How accurately the engine combines signals from multiple sources
- Whether the decision logic can be easily updated when new fraud patterns emerge
Platforms like Sardine, Sift and Kount are popular decisioning engines used across the neobank and fintech space.
How These 11 Techniques Work as a Team
No single fraud detection technique is foolproof. A sophisticated fraudster can sometimes beat one layer. But beating all 11 at the same time? That’s nearly impossible.
The strength of modern fraud detection comes from how these techniques mutually support each other.
ML models catch unusual patterns. Velocity checks stop rapid attacks. Device fingerprinting catches login anomalies. Geolocation flags impossible movements. Behavioral biometrics identifies impostors. Transaction analysis picks up suspicious money flows. Identity verification prevents the creation of fake accounts. AML screening catches dirty money. Social engineering detection helps keep real users from being manipulated. Network analysis exposes organized crime rings. And the decisioning engine brings it all together in real time.
Think of it as a security orchestra — all the instruments playing their parts in unison, working together to produce something no single instrument could achieve alone.
What a Strong Fraud Detection Audit Looks Like
Here is a quick snapshot of what auditors review during a full fraud detection assessment:
| Audit Area | Key Questions Asked |
|---|---|
| ML Models | Is the model trained on up-to-date data? |
| Velocity Controls | Are thresholds set correctly? |
| Device Fingerprinting | Can it identify emulators and VMs? |
| Geolocation | Does it handle VPN users fairly? |
| Behavioral Biometrics | How quickly does it raise a red flag? |
| Transaction Patterns | Can it detect slow-burn fraud? |
| Identity Verification | Is liveness detection reliable? |
| AML Screening | Are watchlists updated in real time? |
| Social Engineering | Are there in-app alerts? |
| Network Analysis | Can it map cross-account fraud? |
| Decisioning Engine | Can it withstand peak load? |
FAQs About Fraud Detection in Neobank Security Audits
Q: How frequently do neobanks upgrade their fraud detection systems? The best neobanks update their ML models and fraud rules continuously — sometimes even weekly. Fraudsters change quickly and detection systems have to keep up.
Q: Is there a risk of fraud detection falsely blocking legitimate users? Yes, and this is called a “false positive.” Any good fraud detection system is calibrated to minimize false positives while still catching actual fraud. Security audits specifically exist to check on this balance.
Q: What is the greatest fraud risk that neobanks face right now? At present, account takeover fraud and APP (Authorized Push Payment) fraud are both devastating threats. Social engineering attacks — where a real person is duped into transferring money — are particularly difficult to stop.
Q: Do small neobanks have the same fraud detection as big ones? Not always. Smaller neobanks may depend more heavily on third-party fraud detection vendors rather than building their own systems. That’s not necessarily a problem — but auditors do verify that vendor solutions are thoroughly integrated and properly configured.
Q: Is behavioral biometrics an invasion of privacy? This is a genuine debate. The information collected is behavioral — not content — but it is personal nonetheless. Legitimate neobanks encrypt and anonymize behavioral data and disclose its use in their privacy policies. Auditors make sure these practices are enforced.
Q: What is the best course of action if I suspect my neobank account has been targeted by fraud? Act immediately. Freeze your account from inside the app. Contact customer support. Change your password and remove any unfamiliar devices. Report the suspicious activity so the fraud team can investigate and protect your funds.
Conclusion: Fraud Never Sleeps — And Neither Should Your Bank’s Defenses
Fraud is not a problem that gets solved once and stays solved. It’s a moving target. As detection improves, fraudsters adapt. As fraudsters adapt, detection has to improve again.
That cycle never stops.
What neobank and digital wallet security audits do is ensure that the platforms people trust with their money are always one step ahead. The 11 fraud detection methods outlined in this article are not hypothetical. They are running right now, in the background, defending real accounts owned by real people.
Understanding that these systems are out there should provide real peace of mind for users. But it’s wise to remain vigilant too. No system is perfect, and the most sophisticated fraud attack is often one that targets you directly — not the technology.
Stay informed. Use strong passwords. Enable MFA. And choose neobanks that take security audits seriously.
Your money deserves nothing less.